All about S3 Backup
Wiki Article
Our Rto Statements
Table of ContentsThe 8-Minute Rule for S3 BackupSome Ideas on Aws Backup You Need To KnowThings about Aws BackupThe Main Principles Of Aws Cloud Backup The 8-Minute Rule for Ec2 BackupThe Main Principles Of Aws Backup
Worldwide authorities have stepped in with regulative compliance like General Data Security Guideline (GDPR). The GDPR emphasizes the personal information rights of EU citizens, consisting of the right to alter, gain access to, eliminate, or transfer their data. Personal data describes any details that connects to an individual. This includes names, physical characteristics, addresses, racial or ethnic attributes, as well as biometric data like DNA and fingerprints.
To keep their information offered whatsoever times, companies require to keep the IT infrastructure energetic even in the case of a calamity. This state of guaranteed access to information is referred to as data availability. This write-up reviews the basics of information accessibility and its challenges, and also offers strategies to maintain a high degree of data schedule.
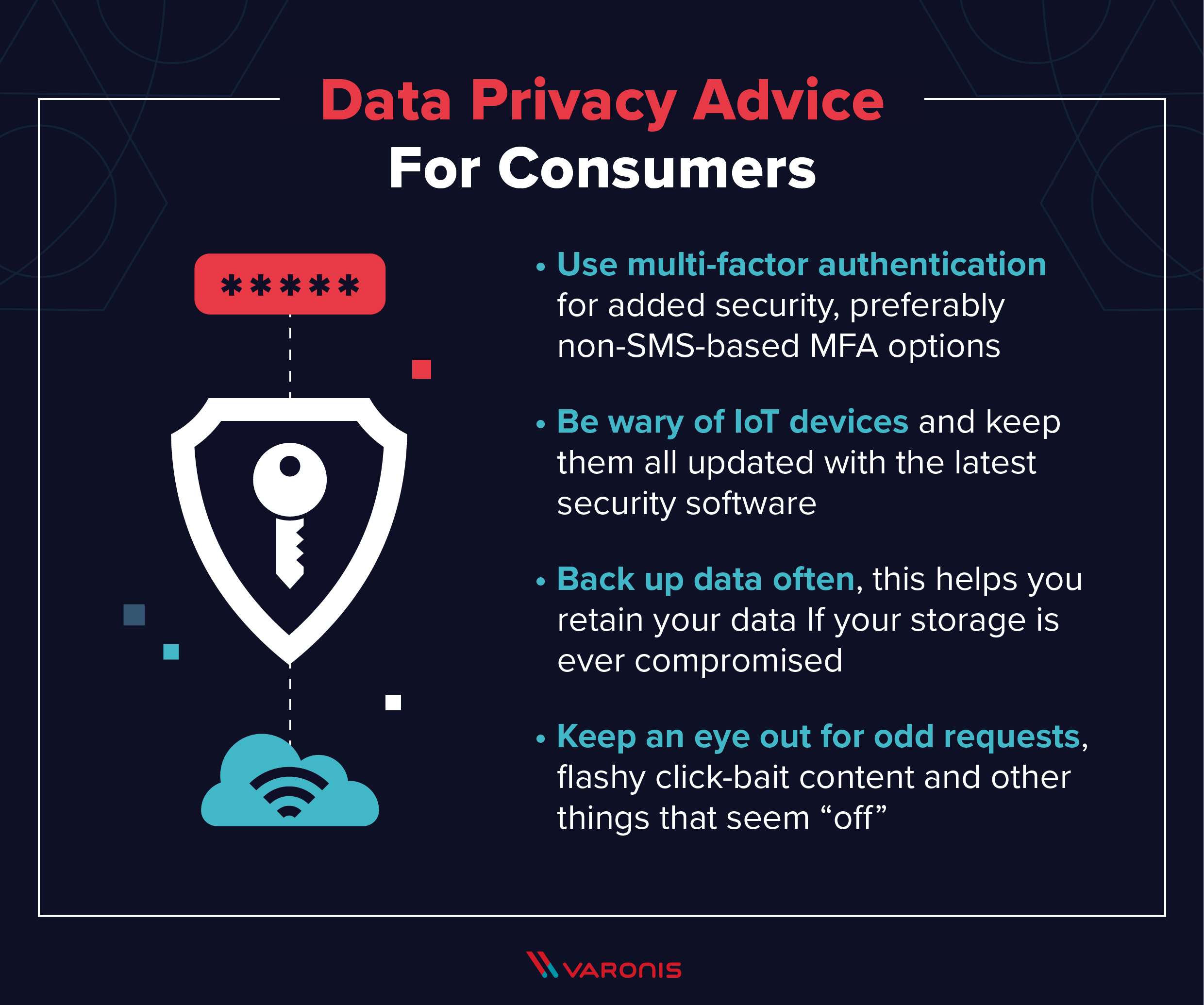
Without an appropriate information protection policy, delicate details can come under the hands of aggressors, allowing them to get access to your network, as well as expose the individual information of clients and workers. This article presents the idea of data safety and the various tools as well as methods you can make use of to secure your information as well as protect against a catastrophe.
Ransomware Protection Can Be Fun For Everyone
File encryption guarantees the integrity of information by shielding it from unapproved modification. Security lowers the danger of accessing information from unreliable resources by verifying data's source.A constant data defense system maintains a document of all data adjustments and allows you to restore a system to any previous time. This kind of backup addresses the problem of losing information developed between 2 scheduled backups. It additionally offers defense versus attacks like ransomware or malware, along with unintentional removal of information.
Any kind of firm that processes and shops personal data of EU people, even if it is not physically situated in the EU, have to put on the GDPR policies. There are 2 main functions in the GDPR: the GDPR Information Cpu is an entity that holds or processes this type of information on part of one more organization, and a GDPR Data Controller that gathers or refines individual information for its own functions.
Object Lock prevents object version deletion throughout a user-defined retention duration. Unalterable S3 objects are shielded utilizing item, or bucket-level arrangement of WORM and retention attributes. This performance gives both information protection, including additional security against unintended or destructive removal along with ransomware and also regulatory conformity. Find out more: S3 Things Lock Protecting Data for Ransomware Dangers as well as Conformity The cloud-based membership of Office 365 allows workers to work anywhere, anytime without the requirement to host their own content and emails.
An Unbiased View of Ransomware Protection
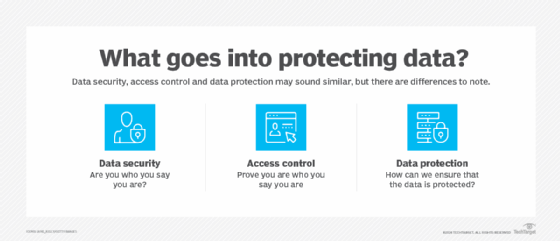
Data security is the procedure of protecting important information from corruption, compromise or loss. The importance of data defense enhances as the amount of information created as well as stored remains to expand at unprecedented prices. There is additionally little resistance for downtime that can make it difficult to accessibility vital information.

The crucial concepts of data security are to safeguard and also make readily available data under all scenarios.
Aws S3 Backup Can Be Fun For Everyone
Data lifecycle management is the procedure of automating the motion of crucial information to online as well as offline storage. Information lifecycle administration is a comprehensive strategy for valuing, cataloging as well as safeguarding details properties from application and also user mistakes, malware and infection attacks, equipment failure or center interruptions and interruptions. More just recently, data administration has actually concerned include locating methods to open business value from or else dormant copies of information for reporting, test/dev enablement, analytics as well as various other purposes.(CDP) backs up all the data in a venture whenever a modification is made. Information portability-- the capacity to move information among various application programs, computing settings or cloud services-- offers another collection of problems as well as solutions for data defense.
Not known Incorrect Statements About Ec2 Backup
Information defense is the you can try these out procedure of protecting essential details from corruption, compromise or loss. The importance of information protection increases as the amount of information developed and also saved proceeds to expand at extraordinary prices. There is likewise little tolerance for downtime that can make it impossible to access important details (https://www.instapaper.com/read/1550606310).Safeguarding data from concession and also guaranteeing data personal privacy are other vital elements of data security. The coronavirus pandemic caused numerous workers to function from house, causing the requirement for remote information security. Businesses have to adapt to guarantee they are shielding data any place workers are, from a main data facility in the office to laptop computers in your home.
The essential principles of data security are to guard and make available data under all scenarios - https://docs.google.com/drawings/d/1FPgfdvuW8xBSarAtJwODOc5ah7N65pVDs5H7iu2jgOQ/edit.
Data lifecycle management is the process of automating the movement of crucial data to online as well as offline storage. Info lifecycle management is an extensive approach for valuing, cataloging and securing details possessions from application and also individual mistakes, malware as well as virus attacks, device failure or center blackouts and also interruptions. A lot more just recently, data management has involved consist of locating ways to open organization worth from or else dormant duplicates of information for reporting, test/dev enablement, analytics and various other functions.
The 10-Minute Rule for Aws S3 Backup
Storage space technologies for safeguarding data consist of a disk or tape back-up that copies assigned details to a disk-based storage space selection or a tape cartridge. Tape-based back-up is a strong alternative for information protection versus cyber strikes. Although accessibility to tapes can be slow-moving, they are portable and inherently offline when not loaded in a drive, and thus safe from risks over a network.Storage space photos can immediately generate a collection of reminders to details saved on tape or disk, making it possible for faster information recuperation, while continual information security (CDP) backs up all the information in an enterprise whenever a modification is made. Data transportability-- the capability to relocate information among various application programs, calculating atmospheres or cloud services-- offers one more set of troubles as well as services for data defense.
Report this wiki page